
Curious: Tor browser official download
| Motivate your gift mp4 download | 831 |
| Download dailymotion videos mp4 free | 584 |
| Free download the spit and the speculum | 243 |
Tor browser official download - that interrupt
Tor (anonymity network)
Tor is free and open-source software for enabling anonymous communication by directing Internet traffic through a free, worldwide, volunteer overlay network consisting of more than seven thousand relays[6] in order to conceal a user's location and usage from anyone conducting network surveillance or traffic analysis. Using Tor makes it more difficult to trace Internet activity to the user: this includes "visits to Web sites, online posts, instant messages, and other communication forms".[7] Tor's intended use is to protect the personal privacy of its users, as well as their freedom and ability to conduct confidential communication by keeping their Internet activities unmonitored.
Tor does not prevent an online service from determining that it is being accessed through Tor. As a result, some websites restrict or even deny access through Tor. For example, Wikipedia blocks attempts by Tor users to edit articles unless special permission is sought.[8]
Onion routing is implemented by encryption in the application layer of a communication protocol stack, nested like the layers of an onion. Tor encrypts the data, including the next node destination IP address, multiple times and sends it through a virtual circuit comprising successive, random-selection Tor relays. Each relay decrypts a layer of encryption to reveal the next relay in the circuit to pass the remaining encrypted data on to it. The final relay decrypts the innermost layer of encryption and sends the original data to its destination without revealing or knowing the source IP address. Because the routing of the communication was partly concealed at every hop in the Tor circuit, this method eliminates any single point at which the communicating peers can be determined through network surveillance that relies upon knowing its source and destination.[9] An adversary may try to de-anonymize the user by some means. One way this may be achieved is by exploiting vulnerable software on the user's computer.[10] The NSA had a technique that targets a vulnerability – which they codenamed "EgotisticalGiraffe" – in an outdated Firefox browser version at one time bundled with the Tor package[11] and, in general, targets Tor users for close monitoring under its XKeyscore program.[12] Attacks against Tor are an active area of academic research[13][14] which is welcomed by the Tor Project itself.[15] The bulk of the funding for Tor's development has come from the federal government of the United States,[16] initially through the Office of Naval Research and DARPA.[17]
The core principle of Tor, "onion routing", was developed in the mid-1990s by United States Naval Research Laboratory employees, mathematician Paul Syverson, and computer scientists Michael G. Reed and David Goldschlag, with the purpose of protecting U.S. intelligence communications online. Onion routing was further developed by DARPA in 1997.[18][19][20][21][22][23]
The alpha version of Tor, developed by Syverson and computer scientists Roger Dingledine and Nick Mathewson[16] and then called The Onion Routing project (which later simply became "Tor", as an acronym for the former name), launched on 20 September 2002.[1][24] The first public release occurred a year later.[25] On 13 August 2004, Syverson, Dingledine, and Mathewson presented "Tor: The Second-Generation Onion Router" at the 13th USENIX Security Symposium.[26] In 2004, the Naval Research Laboratory released the code for Tor under a free license, and the Electronic Frontier Foundation (EFF) began funding Dingledine and Mathewson to continue its development.[16]
In December 2006, Dingledine, Mathewson, and five others founded The Tor Project, a Massachusetts-based 501(c)(3) research-education nonprofit organization responsible for maintaining Tor.[27] The EFF acted as The Tor Project's fiscal sponsor in its early years, and early financial supporters of The Tor Project included the U.S. International Broadcasting Bureau, Internews, Human Rights Watch, the University of Cambridge, Google, and Netherlands-based Stichting NLnet.[28][29][30][31][32]
Prior to 2014, the majority of funding sources came from the U.S. government.[16]
In November 2014 there was speculation in the aftermath of Operation Onymous that a Tor weakness had been exploited.[33] A BBC News source cited a "technical breakthrough"[34] that allowed the tracking of the physical locations of servers. In November 2015 court documents on the matter,[35] besides generating serious concerns about security research ethics[36] and the right of not being unreasonably searched guaranteed by the US Fourth Amendment,[37] may also link the law enforcement operation with an attack on Tor earlier in the year.[35]
In December 2015, The Tor Project announced that it had hired Shari Steele as its new executive director.[38] Steele had previously led the Electronic Frontier Foundation for 15 years, and in 2004 spearheaded EFF's decision to fund Tor's early development. One of her key stated aims is to make Tor more user-friendly in order to bring wider access to anonymous web browsing.[39]
In July 2016 the complete board of the Tor Project resigned, and announced a new board, made up of Matt Blaze, Cindy Cohn, Gabriella Coleman, Linus Nordberg, Megan Price, and Bruce Schneier.[40][41]
Usage[edit]
| Category | % of total | % of active |
|---|---|---|
| Violence | ||
| Arms | ||
| Illicit Social | ||
| Hacking | ||
| Illicit links | ||
| Illicit pornography | ||
| Extremism | ||
| Illicit Other | ||
| Illicit Finance | ||
| Illicit Drugs | ||
| Non-illicit+Unknown | ||
| Illicit total | ||
| Inactive | ||
| Active |
Tor enables its users to surf the Internet, chat and send instant messages anonymously, and is used by a wide variety of people for both licit and illicit purposes.[45] Tor has, for example, been used by criminal enterprises, hacktivism groups, and law enforcement agencies at cross purposes, sometimes simultaneously;[46][47] likewise, agencies within the U.S. government variously fund Tor (the U.S. State Department, the National Science Foundation, and – through the Broadcasting Board of Governors, which itself partially funded Tor until October 2012 – Radio Free Asia) and seek to subvert it.[10][48]
Tor is not meant to completely solve the issue of anonymity on the web. Tor is not designed to completely erase tracks but instead to reduce the likelihood for sites to trace actions and data back to the user.[49]
Tor is also used for illegal activities, e.g., to gain access to censored information, to organize political activities[50] and people additionally use Tor for socially touchy correspondence: talk rooms and web discussions for assault and misuse survivors, or individuals with ailments, or to circumvent laws against criticism of heads of state.[citation needed]
Tor has been described by The Economist, in relation to Bitcoin and Silk Road, as being "a dark corner of the web".[51] It has been targeted by the American National Security Agency and the British GCHQsignals intelligence agencies, albeit with marginal success,[10] and more successfully by the British National Crime Agency in its Operation Notarise.[52] At the same time, GCHQ has been using a tool named "Shadowcat" for "end-to-end encrypted access to VPS over SSH using the Tor network".[53][54] Tor can be used for anonymous defamation, unauthorized news leaks of sensitive information, copyright infringement, distribution of illegal sexual content,[55][56][57] selling controlled substances,[58] weapons, and stolen credit card numbers,[59]money laundering,[60] bank fraud,[61]credit card fraud, identity theft and the exchange of counterfeit currency;[62] the black market utilizes the Tor infrastructure, at least in part, in conjunction with Bitcoin.[46] It has also been used to brick IoT devices.[63]
In its complaint against Ross William Ulbricht of Silk Road, the US Federal Bureau of Investigation acknowledged that Tor has "known legitimate uses".[64][65] According to CNET, Tor's anonymity function is "endorsed by the Electronic Frontier Foundation (EFF) and other civil liberties groups as a method for whistleblowers and human rights workers to communicate with journalists".[66] EFF's Surveillance Self-Defense guide includes a description of where Tor fits in a larger strategy for protecting privacy and anonymity.[67]
In 2014, the EFF's Eva Galperin told BusinessWeek magazine that "Tor’s biggest problem is press. No one hears about that time someone wasn't stalked by their abuser. They hear how somebody got away with downloading child porn."[68]
The Tor Project states that Tor users include "normal people" who wish to keep their Internet activities private from websites and advertisers, people concerned about cyber-spying, users who are evading censorship such as activists, journalists, and military professionals. As of November 2013[update], Tor had about four million users.[69] According to the Wall Street Journal, in 2012 about 14% of Tor's traffic connected from the United States, with people in "Internet-censoring countries" as its second-largest user base.[70] Tor is increasingly used by victims of domestic violence and the social workers and agencies that assist them, even though shelter workers may or may not have had professional training on cybersecurity matters.[71] Properly deployed, however, it precludes digital stalking, which has increased due to the prevalence of digital media in contemporary online life.[72] Along with SecureDrop, Tor is used by news organizations such as The Guardian, The New Yorker, ProPublica and The Intercept to protect the privacy of whistleblowers.[73]
In March 2015 the Parliamentary Office of Science and Technology released a briefing which stated that "There is widespread agreement that banning online anonymity systems altogether is not seen as an acceptable policy option in the U.K." and that "Even if it were, there would be technical challenges." The report further noted that Tor "plays only a minor role in the online viewing and distribution of indecent images of children" (due in part to its inherent latency); its usage by the Internet Watch Foundation, the utility of its onion services for whistleblowers, and its circumvention of the Great Firewall of China were touted.[74]
Tor's executive director, Andrew Lewman, also said in August 2014 that agents of the NSA and the GCHQ have anonymously provided Tor with bug reports.[75]
The Tor Project's FAQ offers supporting reasons for the EFF's endorsement:
Criminals can already do bad things. Since they're willing to break laws, they already have lots of options available that provide better privacy than Tor provides....
Tor aims to provide protection for ordinary people who want to follow the law. Only criminals have privacy right now, and we need to fix that....
So yes, criminals could in theory use Tor, but they already have better options, and it seems unlikely that taking Tor away from the world will stop them from doing their bad things. At the same time, Tor and other privacy measures can fight identity theft, physical crimes like stalking, and so on.
Operation[edit]
Tor aims to conceal its users' identities and their online activity from surveillance and traffic analysis by separating identification and routing. It is an implementation of onion routing, which encrypts and then randomly bounces communications through a network of relays run by volunteers around the globe. These onion routers employ encryption in a multi-layered manner (hence the onion metaphor) to ensure perfect forward secrecy between relays, thereby providing users with anonymity in a network location. That anonymity extends to the hosting of censorship-resistant content by Tor's anonymous onion service feature.[26] Furthermore, by keeping some of the entry relays (bridge relays) secret, users can evade Internet censorship that relies upon blocking public Tor relays.[77]
Because the IP address of the sender and the recipient are not both in cleartext at any hop along the way, anyone eavesdropping at any point along the communication channel cannot directly identify both ends. Furthermore, to the recipient it appears that the last Tor node (called the exit node), rather than the sender, is the originator of the communication.
Originating traffic[edit]
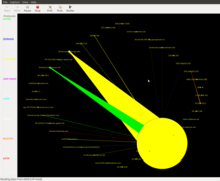
A Tor user's SOCKS-aware applications can be configured to direct their network traffic through a Tor instance's SOCKS interface, which is listening on TCP port 9050 (for standalone Tor) or 9150 (for Tor Browser bundle) at localhost.[78] Tor periodically creates virtual circuits through the Tor network through which it can multiplex and onion-route that traffic to its destination. Once inside a Tor network, the traffic is sent from router to router along the circuit, ultimately reaching an exit node at which point the cleartext packet is available and is forwarded on to its original destination. Viewed from the destination, the traffic appears to originate at the Tor exit node.
Tor's application independence sets it apart from most other anonymity networks: it works at the Transmission Control Protocol (TCP) stream level. Applications whose traffic is commonly anonymized using Tor include Internet Relay Chat (IRC), instant messaging, and World Wide Web browsing.
Onion services[edit]
Tor can also provide anonymity to websites and other servers. Servers configured to receive inbound connections only through Tor are called onion services (formerly, hidden services).[79] Rather than revealing a server's IP address (and thus its network location), an onion service is accessed through its onion address, usually via the Tor Browser. The Tor network understands these addresses by looking up their corresponding public keys and introduction points from a distributed hash table within the network. It can route data to and from onion services, even those hosted behind firewalls or network address translators (NAT), while preserving the anonymity of both parties. Tor is necessary to access these onion services.[80]
Onion services were first specified in 2003[81] and have been deployed on the Tor network since 2004.[82] Other than the database that stores the onion service descriptors,[83] Tor is decentralized by design; there is no direct readable list of all onion services, although a number of onion services catalog publicly known onion addresses.
Because onion services route their traffic entirely through the Tor network, connection to an onion service is encrypted end-to-end and not subject to eavesdropping. There are, however, security issues involving Tor onion services. For example, services that are reachable through Tor onion services and the public Internet are susceptible to correlation attacks and thus not perfectly hidden. Other pitfalls include misconfigured services (e.g. identifying information included by default in web server error responses), uptime and downtime statistics, intersection attacks, and user error.[83][84] The open source OnionScan program, written by independent security researcher Sarah Jamie Lewis, comprehensively examines onion services for numerous flaws and vulnerabilities.[85] (Lewis has also pioneered the field of onion dildonics, inasmuch as sex toys can be insecurely connected over the Internet.)[86]
Onion services can also be accessed from a standard web browser without client-side connection to the Tor network, using services like Tor2web.[87] Popular sources of dark web.onion links include Pastebin, Twitter, Reddit, and other Internet forums.[88]
Nyx status monitor[edit]
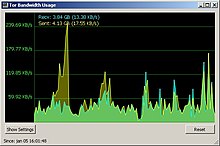
Nyx (formerly ARM) is a command-line status monitor written in Python for Tor.[89][90] This functions much like top does for system usage, providing real time statistics for:
- resource usage (bandwidth, cpu, and memory usage)
- general relaying information (nickname, fingerprint, flags, or/dir/controlports)
- event log with optional regex filtering and deduplication
- connections correlated against Tor's consensus data (ip, connection types, relay details, etc.)
- torrc configuration file with syntax highlighting and validation
Most of Nyx's attributes are configurable through an optional configuration file. It runs on any platform supported by curses including Linux, macOS, and other Unix-like variants.
The project began in the summer of 2009,[91][92] and since 18 July 2010 it has been an official part of the Tor Project. It is free software, available under the GNU General Public License.[93]
Weaknesses[edit]
 | This section needs to be updated. Please update this article to reflect recent events or newly available information.(September 2020) |
Like all current low-latencyanonymity networks, Tor cannot and does not attempt to protect against monitoring of traffic at the boundaries of the Tor network (i.e., the traffic entering and exiting the network). While Tor does provide protection against traffic analysis, it cannot prevent traffic confirmation (also called end-to-end correlation).[94][95]
In spite of known weaknesses and attacks listed here, a 2009 study revealed Tor and the alternative network system JonDonym (Java Anon Proxy, JAP) are considered more resilient to website fingerprinting techniques than other tunneling protocols.
The reason for this is conventional single-hop VPN protocols do not need to reconstruct packet data nearly as much as a multi-hop service like Tor or JonDonym. Website fingerprinting yielded greater than 90% accuracy for identifying HTTP packets on conventional VPN protocols versus Tor which yielded only 2.96% accuracy. However, some protocols like OpenSSH and OpenVPN required a large amount of data before HTTP packets were identified.[96]
Researchers from the University of Michigan developed a network scanner allowing identification of 86% of live Tor "bridges" with a single scan.[97]
Eavesdropping[edit]
Autonomous system (AS) eavesdropping[edit]
If an autonomous system (AS) exists on both path segments from a client to entry relay and from exit relay to destination, such an AS can statistically correlate traffic on the entry and exit segments of the path and potentially infer the destination with which the client communicated. In 2012, LASTor proposed a method to predict a set of potential ASes on these two segments and then avoid choosing this path during the path selection algorithm on the client side. In this paper, they also improve latency by choosing shorter geographical paths between a client and destination.[98]
Exit node eavesdropping[edit]
In September 2007, Dan Egerstad, a Swedish security consultant, revealed he had intercepted usernames and passwords for e-mail accounts by operating and monitoring Tor exit nodes.[99] As Tor cannot encrypt the traffic between an exit node and the target server, any exit node is in a position to capture traffic passing through it that does not use end-to-end encryption such as Secure Sockets Layer (SSL) or Transport Layer Security (TLS). While this may not inherently breach the anonymity of the source, traffic intercepted in this way by self-selected third parties can expose information about the source in either or both of payload and protocol data.[100] Furthermore, Egerstad is circumspect about the possible subversion of Tor by intelligence agencies:[101]
"If you actually look in to where these Tor nodes are hosted and how big they are, some of these nodes cost thousands of dollars each month just to host because they're using lots of bandwidth, they're heavy-duty servers and so on. Who would pay for this and be anonymous?"
In October 2011, a research team from ESIEA claimed to have discovered a way to compromise the Tor network by decrypting communication passing over it.[102][103] The technique they describe requires creating a map of Tor network nodes, controlling one-third of them, and then acquiring their encryption keys and algorithm seeds. Then, using these known keys and seeds, they claim the ability to decrypt two encryption layers out of three. They claim to break the third key by a statistical attack. In order to redirect Tor traffic to the nodes they controlled, they used a denial-of-service attack. A response to this claim has been published on the official Tor Blog stating these rumours of Tor's compromise are greatly exaggerated.[104]
Traffic-analysis attack[edit]
There are two methods of traffic-analysis attack, passive and active. In the passive traffic-analysis method, the attacker extracts features from the traffic of a specific flow on one side of the network and looks for those features on the other side of the network. In the active traffic-analysis method, the attacker alters the timings of the packets of a flow according to a specific pattern and looks for that pattern on the other side of the network; therefore, the attacker can link the flows in one side to the other side of the network and break the anonymity of it.[105] It is shown, although timing noise is added to the packets, there are active traffic analysis methods robust against such a noise.[105]
Steven Murdoch and George Danezis from University of Cambridge presented an article at the 2005 IEEESymposium on security and privacy on traffic-analysis techniques that allow adversaries with only a partial view of the network to infer which nodes are being used to relay the anonymous streams.[106] These techniques greatly reduce the anonymity provided by Tor. Murdoch and Danezis have also shown that otherwise unrelated streams can be linked back to the same initiator. This attack, however, fails to reveal the identity of the original user.[106] Murdoch has been working with and has been funded by Tor since 2006.
Tor exit node block[edit]
Operators of Internet sites have the ability to prevent traffic from Tor exit nodes or to offer reduced functionality for Tor users. For example, it is not generally possible to edit Wikipedia when using Tor or when using an IP address also used by a Tor exit node. The BBC blocks the IP addresses of all known Tor guards and exit nodes from its iPlayer service, although relays and bridges are not blocked.[107]
Bad apple attack[edit]
In March 2011, researchers with the Rocquencourt French Institute for Research in Computer Science and Automation (Institut national de recherche en informatique et en automatique, INRIA), documented an attack that is capable of revealing the IP addresses of BitTorrent users on the Tor network. The "bad apple attack" exploits Tor's design and takes advantage of insecure application use to associate the simultaneous use of a secure application with the IP address of the Tor user in question. One method of attack depends on control of an exit node or hijacking tracker responses, while a secondary attack method is based in part on the statistical exploitation of distributed hash table tracking.[108] According to the study:[108]
The results presented in the bad apple attack research paper are based on an attack in the wild[weasel words] launched against the Tor network by the authors of the study. The attack targeted six exit nodes, lasted for twenty-three days, and revealed a total of 10,000 IP addresses of active Tor users. This study is significant because it is the first documented attack designed to target P2P file-sharing applications on Tor.[108] BitTorrent may generate as much as 40% of all traffic on Tor.[109] Furthermore, the bad apple attack is effective against insecure use of any application over Tor, not just BitTorrent.[108]
Some protocols expose IP addresses[edit]
Researchers from the French Institute for Research in Computer Science and Automation (INRIA) showed that the Tor dissimulation technique in BitTorrent can be bypassed by attackers controlling a Tor exit node. The study was conducted by monitoring six exit nodes for a period of twenty-three days. Researches used three attack vectors:[110]
- Inspection of BitTorrent control messages
- Tracker announces and extension protocol handshakes may optionally contain a client IP address. Analysis of collected data revealed that 35% and 33% of messages, respectively, contained addresses of clients.[110]:3
- Hijacking trackers' responses
- Due to lack of encryption or authentication in communication between the tracker and peer, typical man-in-the-middle attacks allow attackers to determine peer IP addresses and even verify the distribution of content. Such attacks work when Tor is used only for tracker communication.[110]:4
- Exploiting distributed hash tables (DHT)
- This attack exploits the fact that distributed hash table (DHT) connections through Tor are impossible, so an attacker is able to reveal a target's IP address by looking it up in the DHT even if the target uses Tor to connect to other peers.[110]:4–5
With this technique, researchers were able to identify other streams initiated by users, whose IP addresses were revealed.[110]
Sniper attack[edit]
Jansen et al., describes a DDoS attack targeted at the Tor node software, as well as defenses against that attack and its variants. The attack works using a colluding client and server, and filling the queues of the exit node until the node runs out of memory, and hence can serve no other (genuine) clients. By attacking a significant proportion of the exit nodes this way, an attacker can degrade the network and increase the chance of targets using nodes controlled by the attacker.[111]
Heartbleed bug[edit]
The HeartbleedOpenSSL


-
-
-